Category: Security
-
Improve Device Security, Availability, And Cost-Effectiveness With Centralized Device Management
With the increasing proliferation of mobile devices, each requiring its own unique provisioning, configu- ration, and reporting requirements, businesses face enormous challenges ensuring consistency and control over connected devices. IT is responsible for purchasing, setting up, and maintaining mobile de- vices, including printers and other peripherals. IT must ensure that these devices deliver the highest…
-
Understanding Technologies For Creating High-Security ID Cards
Security is an important priority for organizations today more than ever. Having secure access control and identification technologies in place is essential to protecting people and assets. …read more
-
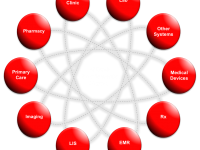
Optimum Healthcare Security Extends From The Door, To Patient Data, To The Cloud
Hospitals face high traffic volumes, complex staffing requirements, and a demanding regulatory environment. Security investment priorities range from protection against active shooter and Infant abduction threats, to compliance with information privacy and other regulations. Meeting these challenges requires best practices for both physical and IT security, using flexible and scalable access control systems that can…
-

Mobile Data Security: Finding The Balance
Bring Your Own Device has changed the rules for corporate security on smartphones and tablets. Companies need to find the right balance in securing email, apps and content without compromising user experience. …read more
-

HHS Reveals Security Risk Assessment Tool
A new security risk assessment (SRA) tool to help guide healthcare providers in small to medium-sized offices conduct risk assessments of their organizations is now available HHS. A new security risk assessment (SRA) tool to help guide healthcare providers in small to medium-sized offices conduct risk assessments of their organizations is now available from the…
-
HHS unveils security risk assessment tool
A new security risk assessment (SRA) tool aimed to help healthcare providers in small to medium sized offices conduct risk assessments of their organizations is now available from the U.S. Department of Health & Human Services. read more …read more
-

Expert panel report on the state of knowledge of food security in northern Canada
A new expert panel report on food security in Northern Canada, has found that food insecurity among northern Aboriginal peoples requires urgent attention in order to mitigate impacts on health and well-being. Aboriginal Food Security in Northern Canada: An Assessment of the State of Knowledge, released today by the Council of Canadian Academies, addresses the…
-

Report: Time to provide nurses with needed mHealth tools
The biggest hospital workforce segment, the nursing staff, is being left out of the mHealth equation by IT organizations concerned about data security, regulatory compliance and inherent costs in… read more …read more
-

A Secure Approach To Healthcare Messaging
Protecting electronic patient health information (e-PHI) has become even more critical as the healthcare industry slowly transitions away from paper-based processes and into a more connected, electronic delivery model. Patient privacy and security is front and center in the Health Insurance Portability and Accountability Act (HIPAA) and Health Information Technology for Economic and Clinical Health…
-

VA vulnerable to cyber attacks, GAO official says
Information security problems have left the U.S. Department of Veterans Affairs vulnerable to cyber attacks, according to testimony presented Tuesday by the Government Accountability Office before the House Committee on Veterans’ Affairs’ subcommittee on oversight and investigations. read more …read more